Blockchain applications to intellectual property (IP) are the current talk of the town. However, there are simpler cryptographic solutions, which IP actors should consider before rushing to distributed ledgers, at least where the aim is to merely notarize IP assets.
Copyright by Sébastien Ragot

The market of blockchain applications to intellectual property is blooming. Blockchain solutions are now routinely proposed for the notarization of IP assets [[i], [ii]] and new platforms emerge, which leverage blockchain technology to create new IP ecosystems [[iii]]. As a result, cryptographic applications to IP are getting the attention of IP professionals again: this time for their own business.
How do these solutions work? Blockchains involve rather complex cryptographic concepts and consensus mechanisms. The matter is complex and admissibly causes misunderstandings, also among IP professionals. Besides, other cryptographic solutions exist, which have comparable advantages and thus deserve the attention of IP professionals too. Therefore, it is time to take stock of the situation and clearly address such solutions, as well as their pros and cons, both technically and legally.
Blockchain explained in less than 700 words
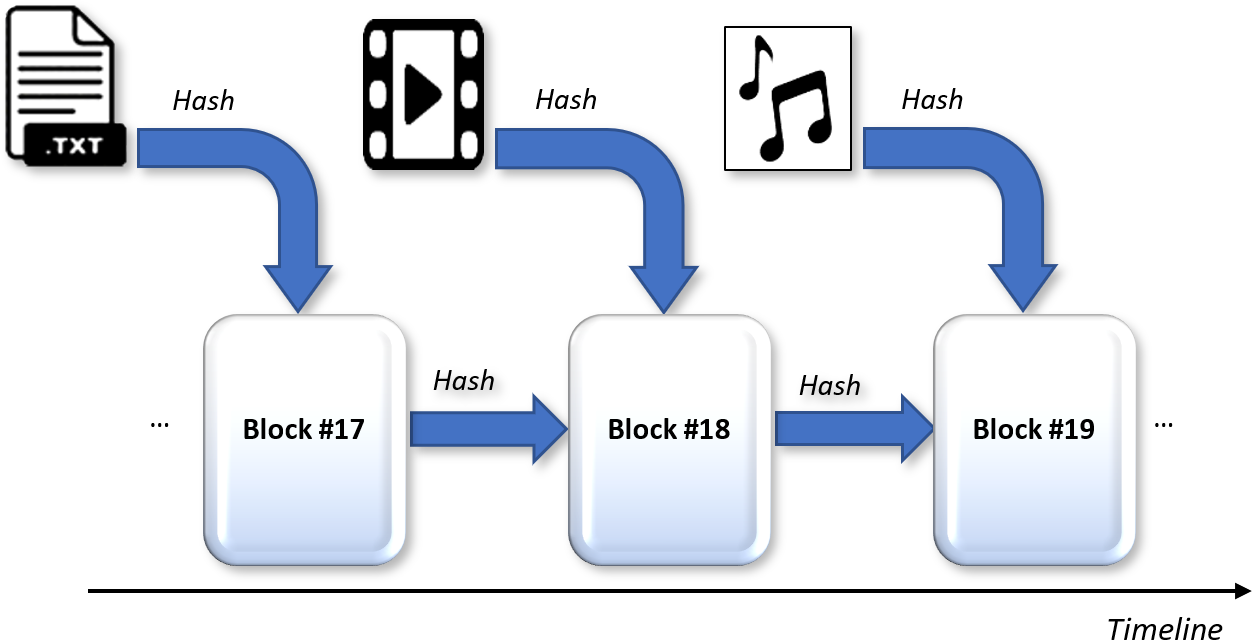
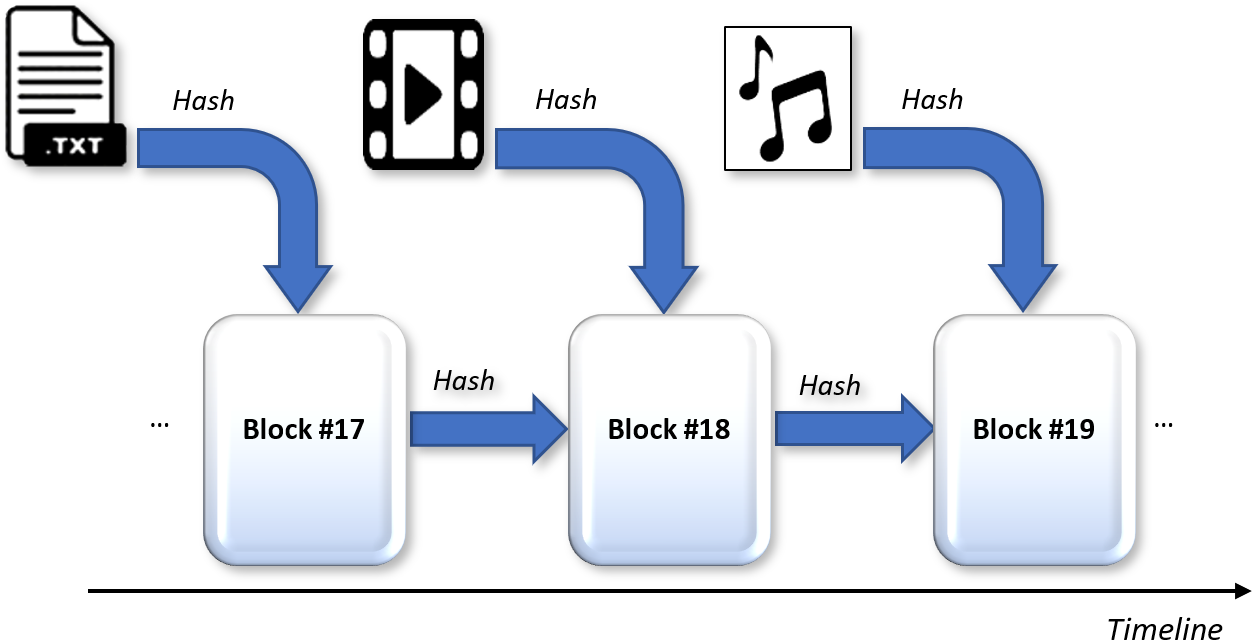
A blockchain is a distributed ledger, i.e., a decentralized database involving several computers that form a computerized network. Thus, records of information are not stored in a single place and, with an adequate set-up, are not under control of a single entity. Basically, a blockchain progressively stores new records of data in blocks that are linked using cryptography. I.e., each new block includes a digital fingerprint (a cryptographic hash) of a previous block. This way, each new block is linked to a previous block, which eventually forms a chain of blocks. Each block is further timestamped, which allows its contents to be notarized, hence the benefits for IP assets. E.g., a blockchain may be used as a registry of IP rights, to store and catalogue original works.

An aspect that is often misunderstood is that data does not need be stored in unencrypted form in a blockchain (they better not be). Rather, data is typically hashed, i.e., transformed via a cryptographic hash function that reduces any input data to a unique cryptic string of fixed size. The string obtained is called “hash value” or simply “hash”. The input data can be of any type and any length: it may for example be an entire text document (even a book), a song, or a video.
Thank you for reading this post, don't forget to subscribe to our AI NAVIGATOR!
Hash values of the input data can be compared to fingerprints of humans. The hash function is a “one-way function”, meaning it is practically infeasible to invert. Likewise, it is not possible to identify a human from a sole fingerprint (at least not without a list of indexed fingerprints). Different inputs to a hash function yield distinct hash values but a same input always leads to the same hash value, just like fingerprints are unique to every individual person. Thus, one cannot obtain the initial input data from its sole hash value but one can easily compare hash values of different files: if the files differ, their hash values differ as well, subject to very improbable collisions between the two hash values. Accordingly, hash values can safely be logged on a blockchain, without disclosing the initial data used to obtain them. […]
Read the whole article.
Blockchain applications to intellectual property (IP) are the current talk of the town. However, there are simpler cryptographic solutions, which IP actors should consider before rushing to distributed ledgers, at least where the aim is to merely notarize IP assets.
Copyright by Sébastien Ragot
The market of blockchain applications to intellectual property is blooming. Blockchain solutions are now routinely proposed for the notarization of IP assets [[i], [ii]] and new platforms emerge, which leverage blockchain technology to create new IP ecosystems [[iii]]. As a result, cryptographic applications to IP are getting the attention of IP professionals again: this time for their own business.
How do these solutions work? Blockchains involve rather complex cryptographic concepts and consensus mechanisms. The matter is complex and admissibly causes misunderstandings, also among IP professionals. Besides, other cryptographic solutions exist, which have comparable advantages and thus deserve the attention of IP professionals too. Therefore, it is time to take stock of the situation and clearly address such solutions, as well as their pros and cons, both technically and legally.
Blockchain explained in less than 700 words
A blockchain is a distributed ledger, i.e., a decentralized database involving several computers that form a computerized network. Thus, records of information are not stored in a single place and, with an adequate set-up, are not under control of a single entity. Basically, a blockchain progressively stores new records of data in blocks that are linked using cryptography. I.e., each new block includes a digital fingerprint (a cryptographic hash) of a previous block. This way, each new block is linked to a previous block, which eventually forms a chain of blocks. Each block is further timestamped, which allows its contents to be notarized, hence the benefits for IP assets. E.g., a blockchain may be used as a registry of IP rights, to store and catalogue original works.
An aspect that is often misunderstood is that data does not need be stored in unencrypted form in a blockchain (they better not be). Rather, data is typically hashed, i.e., transformed via a cryptographic hash function that reduces any input data to a unique cryptic string of fixed size. The string obtained is called “hash value” or simply “hash”. The input data can be of any type and any length: it may for example be an entire text document (even a book), a song, or a video.
Thank you for reading this post, don't forget to subscribe to our AI NAVIGATOR!
Hash values of the input data can be compared to fingerprints of humans. The hash function is a “one-way function”, meaning it is practically infeasible to invert. Likewise, it is not possible to identify a human from a sole fingerprint (at least not without a list of indexed fingerprints). Different inputs to a hash function yield distinct hash values but a same input always leads to the same hash value, just like fingerprints are unique to every individual person. Thus, one cannot obtain the initial input data from its sole hash value but one can easily compare hash values of different files: if the files differ, their hash values differ as well, subject to very improbable collisions between the two hash values. Accordingly, hash values can safely be logged on a blockchain, without disclosing the initial data used to obtain them. […]
Read the whole article.
Share this: