Deep learning is gaining prominence in the field of artificial intelligence, streamlining processes, and bringing huge financial gains to businesses. However, businesses must be aware of deep learning challenges before they employ deep learning to solve their problems.
copyright by www.bbntimes.com

Deep learning is everywhere. From your Google voice assistant to your ‘Netflix and chill’ recommendations to the very humble Grammarly — they’re all powered by deep learning. Deep learning has become one of the primary research areas in artificial intelligence. Most of the well-known applications of artificial intelligence, such as image processing, speech recognition and translations, and object identification are carried out by deep learning. Thus, deep learning has the potential to solve most business problems, streamlining your work procedures, or creating useful products for end customers. However, there are certain deep learning challenges that you should be aware of, before going ahead with business decisions involving deep learning.
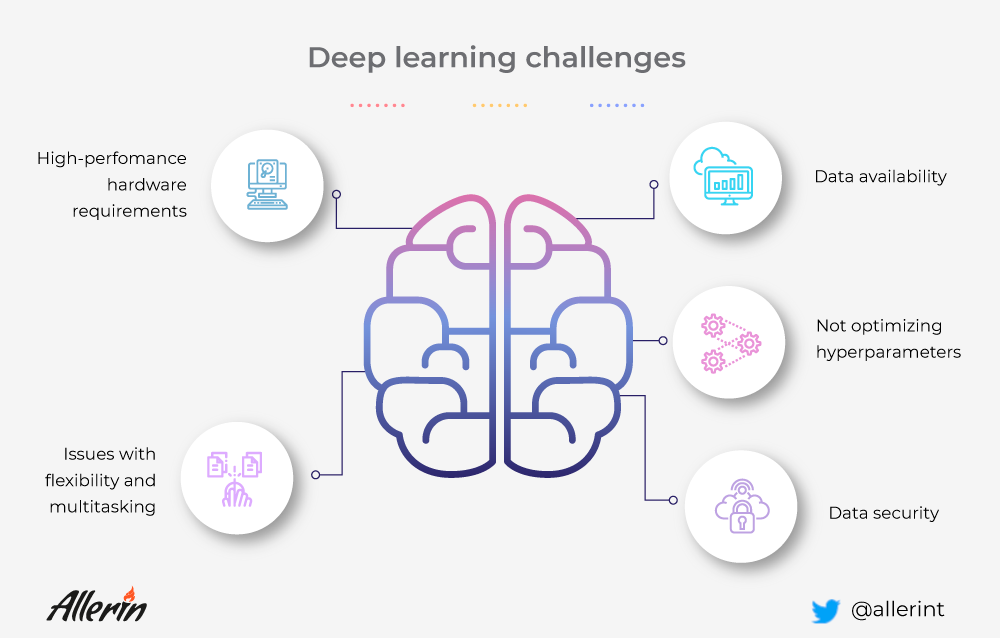
Here are 5 deep learning challenges to watch out for:
Deep learning, although useful in creating solutions has certain limitations that can affect the output of the deep learning model and not provide the intended results. Some of the challenges businesses may encounter are:
1. Data Availability
Deep learning models require tons of data to train. Additionally, the quality of the data, too, matters along with the quantity. A deep learning model with insufficient or low-quality data will not perform efficiently. The output may be vastly different than what it was intended to produce. Errors in the output of a deep learning model with low quantity and bad-quality data are common. The time required for the neural network to train itself, too, will be high in such instances. Thus, your business will end up exhausting time, money, and resources without any fruitful results, leading to disappointments.
You must, therefore, ensure that the deep learning model you wish to train and use has sufficient and appropriate data before proceeding with the solution. Generally, data is easily available for commercial applications like a smartphone app that needs to be rolled out for millions of users. But data is hard to come-by for industrial applications. Thus, if your business is looking to develop industry-specific solutions based on deep learning models, you must ensure that you have a sufficient quantity of data available with you. For example, a speech translation program will require data from multiple demographics, dialects, and age groups. Terabytes of data are required to train the deep learning model to learn and understand a single language. To train it to translate to another language is another task altogether, requiring even more time and datasets. Gathering data for such systems may be difficult in the beginning, but can become progressively easy when multiple users provide data in the form of feedback. Similarly, a solution developed to monitor and automate manufacturing data using a deep learning model requires large datasets specific to the manufacturing sector for the solution to be successful. Such data is hard to come by as it is highly use-case oriented.
2. Data Security
Machine learning systems are employed for training neural networks in a deep learning model. In a business context, providing training datasets to such models and systems requires sensitive and real-world business information to be fed to the system. Therefore, if you’re implementing deep learning models, you must ensure that the data used in training is not compromised at any cost. Hackers can plan adversarial attacks on the neural networks that can affect the output of the deep learning program. This can fool the deep-learning models and can significantly change the output desired from the model. Such adversarial attacks can even get hackers to access sensitive information regarding your business operations and can be used wrongfully for monetary gains or for tarnishing the reputation of the organization.
For example, a deep learning model for classifying images into different classes relies on images for training. Hackers can add random noise to certain images in the training dataset that can alter the analysis and training process of the deep learning model. It will eventually result in the program being inefficient.
Hackers can add random noise to a deep learning model that classifies animals into horses or zebras. The additional malicious information may result in the deep learning model to identify horses as zebras and vice versa. Thus, the deep learning model is of no use and needs to be fed again with new datasets and retrained. This leads to the wastage of time and resources and delays the deployment of the product. Other adversarial attacks may result in sensitive information being accessed by hackers which can compromise the integrity of the organization. […]
Thank you for reading this post, don't forget to subscribe to our AI NAVIGATOR!
read more – by www.bbntimes.com
Deep learning is gaining prominence in the field of artificial intelligence, streamlining processes, and bringing huge financial gains to businesses. However, businesses must be aware of deep learning challenges before they employ deep learning to solve their problems.
copyright by www.bbntimes.com

Deep learning is everywhere. From your Google voice assistant to your ‘Netflix and chill’ recommendations to the very humble Grammarly — they’re all powered by deep learning. Deep learning has become one of the primary research areas in artificial intelligence. Most of the well-known applications of artificial intelligence, such as image processing, speech recognition and translations, and object identification are carried out by deep learning. Thus, deep learning has the potential to solve most business problems, streamlining your work procedures, or creating useful products for end customers. However, there are certain deep learning challenges that you should be aware of, before going ahead with business decisions involving deep learning.
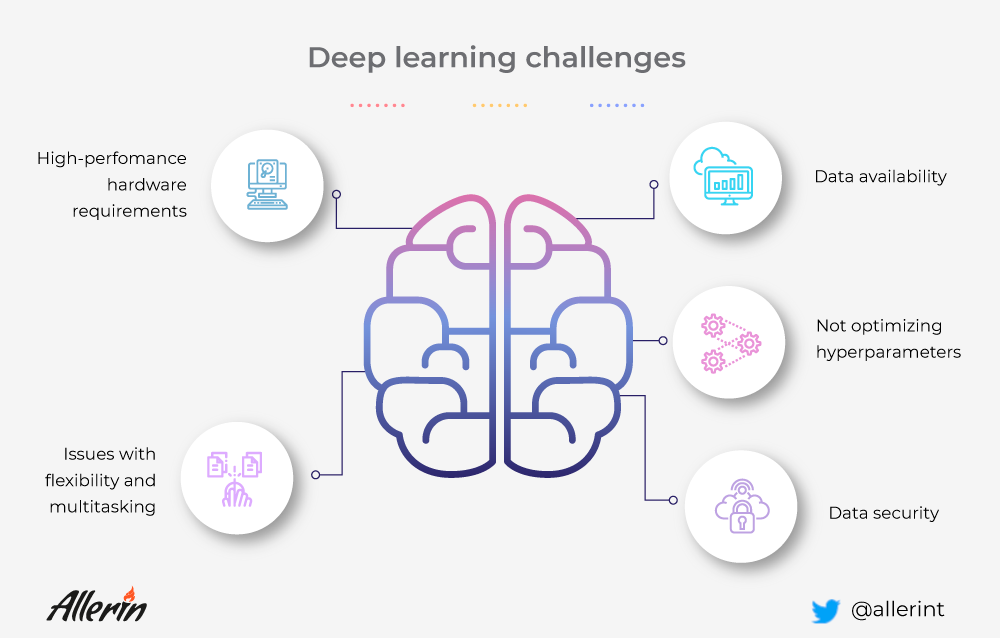
Here are 5 deep learning challenges to watch out for:
Deep learning, although useful in creating solutions has certain limitations that can affect the output of the deep learning model and not provide the intended results. Some of the challenges businesses may encounter are:
1. Data Availability
Deep learning models require tons of data to train. Additionally, the quality of the data, too, matters along with the quantity. A deep learning model with insufficient or low-quality data will not perform efficiently. The output may be vastly different than what it was intended to produce. Errors in the output of a deep learning model with low quantity and bad-quality data are common. The time required for the neural network to train itself, too, will be high in such instances. Thus, your business will end up exhausting time, money, and resources without any fruitful results, leading to disappointments.
You must, therefore, ensure that the deep learning model you wish to train and use has sufficient and appropriate data before proceeding with the solution. Generally, data is easily available for commercial applications like a smartphone app that needs to be rolled out for millions of users. But data is hard to come-by for industrial applications. Thus, if your business is looking to develop industry-specific solutions based on deep learning models, you must ensure that you have a sufficient quantity of data available with you. For example, a speech translation program will require data from multiple demographics, dialects, and age groups. Terabytes of data are required to train the deep learning model to learn and understand a single language. To train it to translate to another language is another task altogether, requiring even more time and datasets. Gathering data for such systems may be difficult in the beginning, but can become progressively easy when multiple users provide data in the form of feedback. Similarly, a solution developed to monitor and automate manufacturing data using a deep learning model requires large datasets specific to the manufacturing sector for the solution to be successful. Such data is hard to come by as it is highly use-case oriented.
2. Data Security
Machine learning systems are employed for training neural networks in a deep learning model. In a business context, providing training datasets to such models and systems requires sensitive and real-world business information to be fed to the system. Therefore, if you’re implementing deep learning models, you must ensure that the data used in training is not compromised at any cost. Hackers can plan adversarial attacks on the neural networks that can affect the output of the deep learning program. This can fool the deep-learning models and can significantly change the output desired from the model. Such adversarial attacks can even get hackers to access sensitive information regarding your business operations and can be used wrongfully for monetary gains or for tarnishing the reputation of the organization.
For example, a deep learning model for classifying images into different classes relies on images for training. Hackers can add random noise to certain images in the training dataset that can alter the analysis and training process of the deep learning model. It will eventually result in the program being inefficient.
Hackers can add random noise to a deep learning model that classifies animals into horses or zebras. The additional malicious information may result in the deep learning model to identify horses as zebras and vice versa. Thus, the deep learning model is of no use and needs to be fed again with new datasets and retrained. This leads to the wastage of time and resources and delays the deployment of the product. Other adversarial attacks may result in sensitive information being accessed by hackers which can compromise the integrity of the organization. […]
Thank you for reading this post, don't forget to subscribe to our AI NAVIGATOR!
read more – by www.bbntimes.com
Share this: